Excel brojanje jedinstvenih ćelija
Napomena : Ovaj metod NE FUNKCIONIŠE za više od par hiljada podataka! Ima dve različite definicije različitosti (nas interesuje druga)...
HowTo za Linux, WIN, Heklanje i Kuhinjske recepte. Prodaja hekleraja :-)
Napomena : Ovaj metod NE FUNKCIONIŠE za više od par hiljada podataka! Ima dve različite definicije različitosti (nas interesuje druga)...
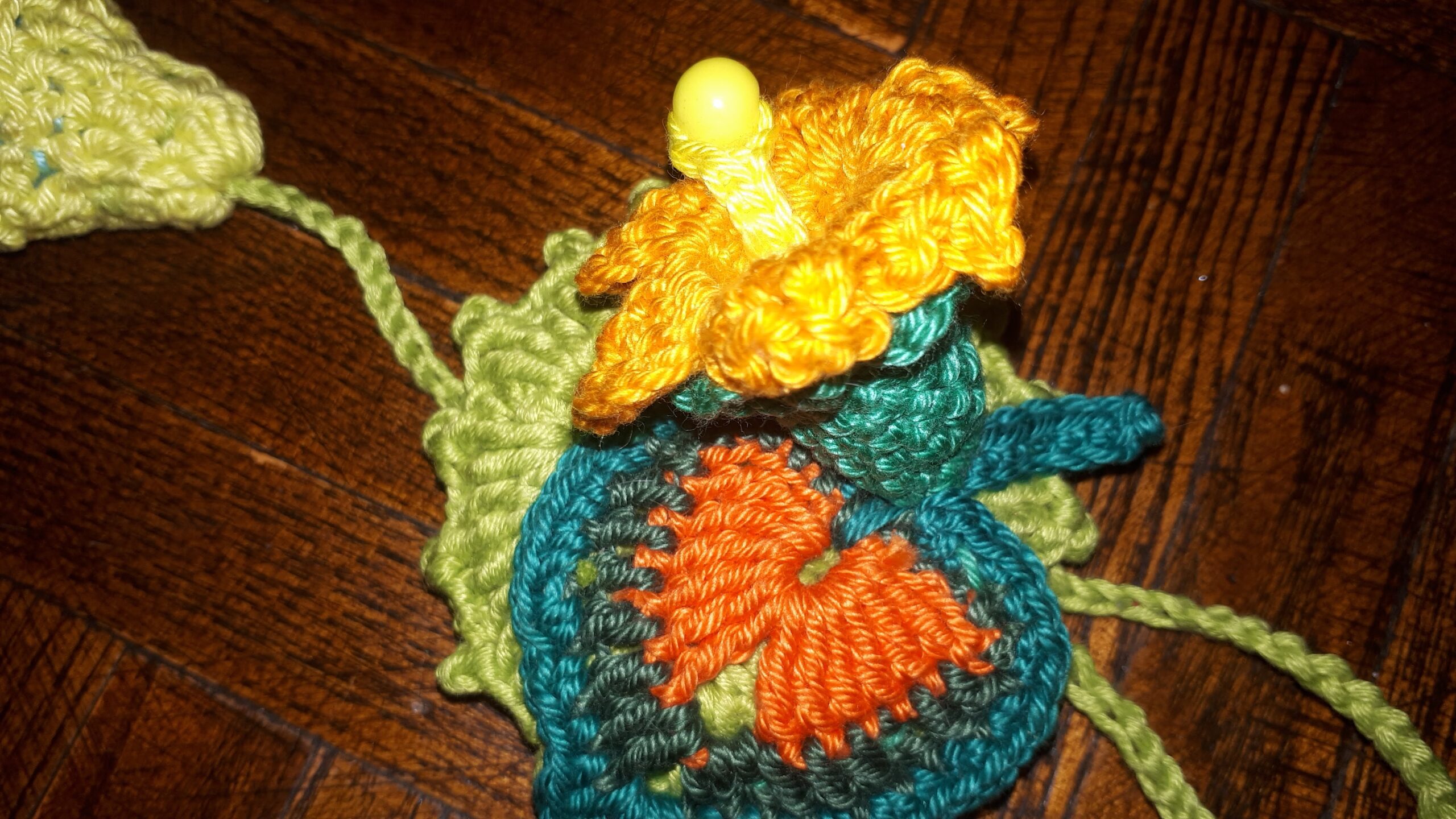
Ja zapela i heklam uskršnja jaja :-) PS u prirodi mnogo bolje izgledaju! Ovo jaje je malo Japanski inspirisano :...
Meni je baš zabavno da ih heklam, a lepa su dekoracija :
Staklene tegle za sadnice da puste korenje, pre presađivanja u saksiju. Ispalo je sjajno!
Heklana balaklava ili ski maska za hladno vreme. Sa zakašnjenjem, ali biće za sledeću godinu :-)
Isheklala sam gomilu manjih i većih vrećica, sa cvetićima, zmajskim krljuštima, srcićima, i bobicama, i sjajno je ispalo. Podelila ih...
Koristiti Access ako VBA u Excel-u nije u stanju da uradi obradu (ako su dve nested petlje sa iole više...
Paziti, VBA se zaglavi ako su veliki brojevi u pitanju! Private Sub CommandButton1_Click() Dim partijar As Long Dim partijae As...
Lokacija slika za Android telefon Redmi Note 12s za aplikaciju WatsApp : This PC\Redmi Note 12S\Interner gemeinsamer Speicher\Android\media\com.whatsapp\WhatsApp\Media\WhatsApp Images Lokacija...
Ne treba online konverter ili tako nešto :-) 1. Open the JPG file you want to convert (otvoriti sa bilo...






